Similarities, Differences, and Everything You Need to Know About GDPR and HIPAA Compliance


If your company leverages digital tools it means that you have to comply with the regulations of the region you work in. For example, if you are gathering, storing, or processing the personal information of European Union (EU) residents, you have to adhere to the GDPR privacy regulations. Likewise, businesses in the healthcare sector in the US have to adhere to HIPAA federal laws.
But, are GDPR vs HIPAA requirements the same? And how do you ensure GDPR and HIPAA-compliant data collection?
At Go Wombat, we pay particular attention to the compliance of the software we create with appropriate regulations, depending on the geographic region. In this article, we’ll share the differences between GDPR and HIPAA compliance. We’ll also share tips to help your company comply with either or both of them.
HIPAA vs GDPR: What are they?
In simple terms, HIPAA and GDPR are two sets of regulations that impact the way certain companies and websites have to handle data.
We’ll dive into the nitty gritty of each one of these two in the next section.
But, before that, we wanted to take a moment to highlight the fact that both regulations were created for similar purposes. Namely, to create a safety standard and regulate how businesses handle personal identifiable information.
This is the reason why many businesses assume there’s a connection between the two, when in reality they are independent of each other.
GDPR and HIPAA Compliance Compared
While there are instances where a business has to adhere to both HIPAA and GDPR regulations, it heavily depends on the data being handled. At the same time, the location of the owner of the information also plays a key role.
Let’s take a closer look at each of these.
Health Insurance Portability and Accountability Act (HIPAA)
Health Insurance Portability and Accountability Act, or HIPAA, is a US federal law that contains rules for medical information exchange, including how it should be handled, who has access to it, and so on.
The law was adopted in 1996 and applies to hospitals, doctors’ offices, and other establishments where patient information is collected, or where healthcare services are provided. These regulations affect both paper and electronic information.
The goals of HIPAA compliance
HIPAA is based on two essential principles of patient care: privacy and confidentiality.
Privacy implies that any individual has the right to restrict access to their medical information.
Confidentiality means that healthcare specialists must store the information correctly and go the extra mile to prevent unauthorised third-party access.
Thus, the law specifies only people involved in the healthcare sector or other designated individuals are allowed to see this information.
The collected data cannot be disclosed without a patient's consent, except for cases when it is required under law or for specific clinical reasons.
General Data Protection Regulation (GDPR)
GDPR or General Data Protection Regulation is a data protection law that covers all sectors, including healthcare. The laws of GDPR are international that became enforceable on 25 May 2018.
Although it was adopted in the EU, GDPR laws cover all countries that work with the personal data of EU residents, including foreign citizens.
The goals of GDPR compliance
The law provides the protection of the user data on the internet by regulating the transfer, processing, and storage of personal data of individuals located on the EU territory, or an EU citizen.
It is crucial to identify what personal data means under the umbrella of GDPR protection.
According to GDPR, personal data is any information related to the data subject (individual) that can be identified. An identified individual is a person who has been linked to a set of connected information (name, phone number, login, email, ID, and so on).
Who do GDPR laws apply to?
The international status allows the law to extend beyond the EU territory. If the entity uses resources within the EU territory or the individual is an EU citizen currently located in another region, the law still applies in both cases and provides protection for the user.
This means that all US organisations that process, gather, or store the personal information of EU residents, including those in compliance with HIPAA regulations, must follow the GDPR law.
In other words, any entity that performs specific operations in the EU, offers goods or services to people in the EU, or monitors the behaviour of EU residents must comply with all the GDPR rules.
Compliance with local regulations is not only legal, it is crucial. Contact us to get detailed consulting services!
Key differences between GDPR and HIPAA
Even though both laws protect personal information, GDPR is a much broader law than HIPAA. Furthermore, GDPR more strictly applies to personal information protection, rather than medical records that already carry a degree of confidentiality.
Let’s take a closer look at the three main differences between HIPAA and GDPR.
Consent
According to HIPAA, some PHI (personal health information) can be disclosed without the patient's consent.
For example, under HIPAA, healthcare organisations can send PHI to other healthcare providers for treatment purposes.
Also, in case of emergencies (urgent surgical procedures.), healthcare providers may disclose PHI without patient consent.
Under GDPR, any PHI cannot be disclosed without explicit patient consent. The same applies to any marketing and communication activities between the healthcare provider and the data owner.
Right to be forgotten
This right is available under GDPR, while HIPAA doesn’t contain this rule.
The right to be forgotten means that any user may request a company or organisation that’s collected data to erase their personal data.
Under the GDPR, companies that collect information from EU users need to have a system in place to receive, process, and notify users about this process.
Data breaches
Suffering a data breach is a severe problem so businesses need to take steps to avoid this issue, especially if they process HIPAA-protected data.
The HIPAA Breach Notification Rule stipulates that all healthcare providers must notify individuals if their unsecured PHI is breached or leaked.
If more than 500 individuals were affected, but it is also required to notify the OCR (office of civil rights) of the U.S. Department of Health & Human Services within 60 days. In case of more minor breaches, it is necessary to notify the OCR by March 1 of the following year.
Under GDPR, all companies must notify the regulatory body about the data breach within 72 hours, regardless of the number of affected individuals.
HIPAA makes GDPR compliance easier
If your website or organisation is already HIPAA compliant, it means that you have different safeguards in place to protect patient data.
This, in turn, means that you’re that much closer to becoming GDPR compliant, which is crucial if you want to or already collect information from EU residents.
At Go Wombat, we can create custom software solutions that comply with HIPAA, GDPR, or both of these regulations. Moreover, we can also make sure that your software meets any other requirement set forth by the law or by your internal processes.
How do we follow GDPR when creating software?
Go Wombat is an international software development company, but we’ve built countless solutions for clients in Europe. Thus far, it has been vital to ensure that all relevant projects we create comply with the GDPR guidelines.
At Go Wombat, we have a CISO (Chief Information Security Officer) responsible for the software compliance process, and he is a certified DPO.
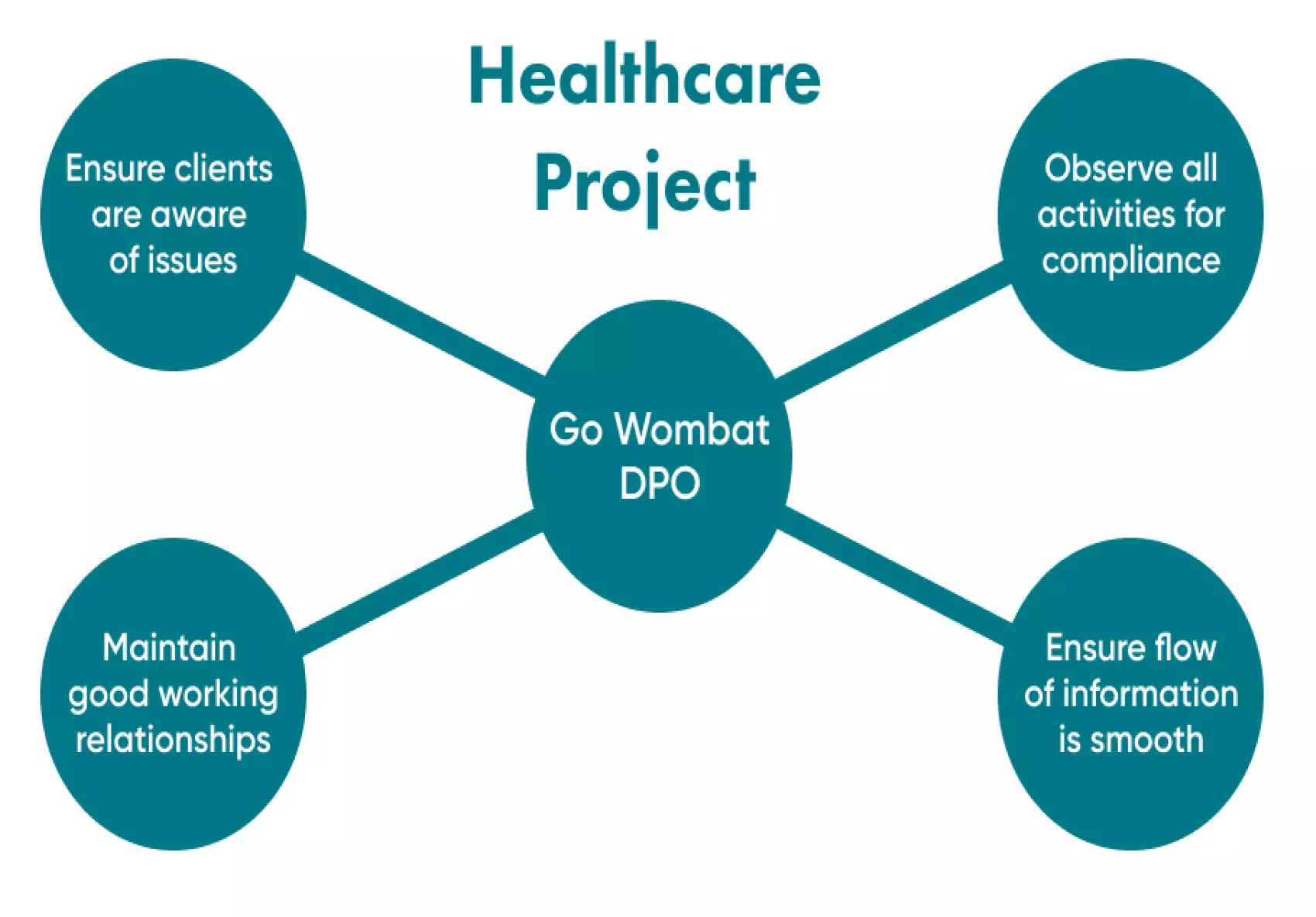
What is the DPO?
DPO stands for data protection officer, and this is a specialist in charge of carrying out regular security audits, training employees, and monitoring compliance with the GDPR privacy rules.
The main task of the DPO is to ensure that all sensitive information is protected adequately from unauthorised access. Furthermore, if the company violates the process of gathering and processing personal data, the DPO must notify the supervisory authority about it.
The DPO is fully qualified to ensure compliance with the GDPR.
At Go Wombat, we help our team members grow because we understand the value of having highly-skilled individuals. This is the case with our CISO, who obtained full DPO certification after joining the Go Wombat team.
So, what is the scope of activity of the Data Protection Officer at Go Wombat?
-
Definition of the project type and identifies what personal data can be used there.
-
Determination of the scope of personal data use
-
Performance of data protection impact assessment.
-
Creation of the matrix of responsibilities
-
Finally, when the project is developed, the DPO verifies everything to make sure that all personal data is processed and transferred (or not simply stored) correctly.
The process of technical compliance with GDPR at Go Wombat
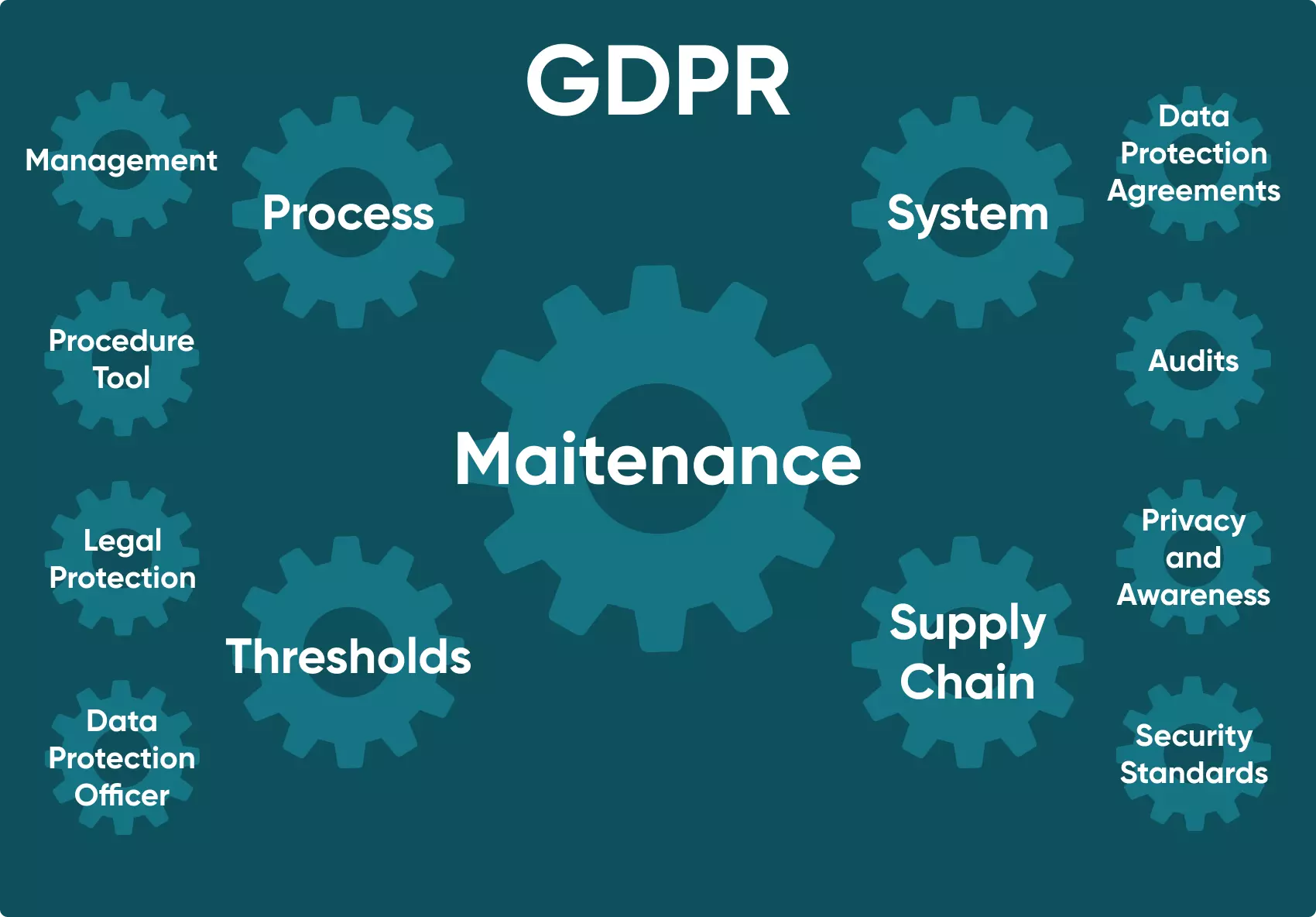
Most projects we create involve consumer personal data, since even email is referred to as identifiable information.
Our specialists analyse what PII (Personally Identifiable Information) we receive, and then it is necessary to study all the requirements.
The next step is to follow Article 32 under the GDPR, which stipulates the use of technical measures to protect personal information.
These measures include many stages, but we’ll cover the most important ones below.
Data anonymisation
Anonymised data cannot be identified without supply data or key tables. Individual usernames are an excellent example of anonymised data.
For starters, usernames should be stored in a separate database. This is to avoid the comparison of the username with its email address.
We follow the best option, which means the creation of UUIDs (Universally Unique Identifiers) for each user. Each UUID is a range of digits, so there is no name or surname. Instead, every user has its own UUID making it impossible to identify the person without the table containing additional data.
Encryption
Encryption is the process of storing data in a way that it cannot be read or otherwise accessed without a key or master key. One of the best ways to ensure this is to use an RDS (Related Database System) from AWS in the European region.
That’s one of the ways we handle this challenge at Go Wombat.
According to Article 32, AWS RDS allows us to ensure that encryption keys and databases are stored on different servers. So, if there is a database leakage, but there are no keys — it is impossible to access the stored information.
So RDS makes it possible to store everything separately.
Then, the following mandatory step includes creating recovery points in case of any unforeseen incidents. We enforce backup systems to ensure the stable performance of the software.
For example, if the system is down due to a DDoS attack, a recovery point enables the restoration of regular functionality, so users have uninterrupted access to the software.
Accountability
As part of the GDPR compliance regulations, companies must monitor all personal data transfers, plus they need to know when and where all data is used.
Go Wombat logs all accesses and users’ activities with the help of AWS CloudWatch.
As you saw above, according to GDPR, each user has the right to be forgotten, so we should have all activities in one place to delete them upon request.
Logs turn into anonymous UUIDs mentioned above, and PII is not used anymore.
Data transfer encryption
Under GDPR, we need to ensure secure data transfer, so we use SSL protocols (Secure Socket Layer) to encrypt the data transferred between resources.
Confidentiality compliance
The last step, but certainly not the least, is to build a strict access system for personal data.
Our team never works directly with personal data during development. Instead, we get blank tables and populate them with random data to test them.
This is crucial since we aim to secure confidential data and avoid any disclosures. Therefore, we don’t use personal data unless we need it for specific reasons or bug fixing, both of which must be agreed upon with a controller.
The expertise of Go Wombat: Summarising one of our healthcare projects
In this section, we’ll provide a bit of insight into a project that meets GDPR and HIPAA compliance.
The project’s goal is to store patients’ records and health conditions. Physicians can use the platform to update patients’ status, and keep information on appointments, procedures, or prescriptions.
Also, the system can synchronise with remote sensors and receive real-time information about health markers like saturation, glucose level, heart rate, and other indicators.
How did we create it?
Amazon services help us ensure compliance with HIPAA and GDPR.
The first one is RDS, where we had our database that also features duplication and encryption features.
The second service is AWS Cognito. We used this one for registration/authorisation, and it still keeps users’ passwords and access tokens today.
At the same time, we also used access tokens rather than specific GDPR and HIPAA personal information when regular repeated access was required.
This token is a type of password and it is used in case of a breach. Which, in turn, ensures the integrity of the personal information.
Additionally, we implemented data anonymisation on the server at the users’ request.
Different time intervals are determined for data storage and anonymisation, so data is not deleted immediately — its deletion is performed depending on HIPAA-specific requirements.
Unlock Success with Premium Software Development
Contact us


GDPR vs HIPAA compliance: Drawing the line
Go Wombat ensures the compliance of its projects, whether it's to GDPR, HIPAA, or any other regulations.
Our CISO is continuously developing his skills, working on cybersecurity issues, making new software more secure, and preventing data leakage.
We also have a recent article about cybersecurity importance — we recommend you read it.
Now, you know the difference between HIPAA and GDPR compliance.
You’ve also seen how we follow GDPR compliance vs HIPAA regulations to help guarantee the integrity and security of our software.
If you are still hesitant and have any questions — feel free to ask us.
Contact us to find out more about project security!
How can we help you ?







